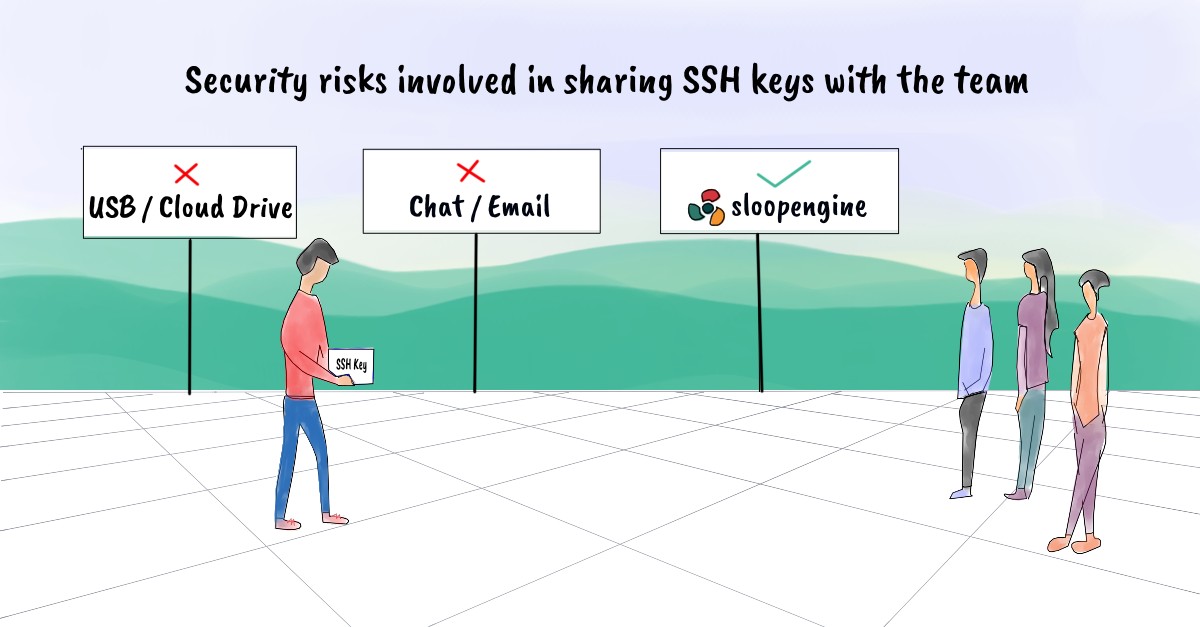
Security risks involved in sharing SSH keys with the team
If you work for an organization that handles a vast number of servers, you'll also have to manage SSH access. On the other hand, maintaining SSH keys is exceedingly difficult for a system administrator or manager. These days, all organizations use the SSH protocol to enable server access to their team members. Usually, SSH key-based authentication is preferred over SSH password-based authentication because SSH key-based authentication is secure and safer than SSH password-based authentication. Finally, everything comes down to managing SSH key pairs. In this blog post, you will learn the potential security risks involved when sharing SSH keys with your team members to provide SSH access.
Thus sharing SSH keys with team members is unavoidable for any kind of organization.
Don't share SSH keys using a cloud drive or USB drive
It is common to see people sharing SSH keys using a USB drive/cloud drive with the team members, but they are unaware of the possible security risks involved. Many possible scenarios can harm your organization/business if you continue this practice further. What will you do in the following situations?
- What happens if you lose the disk drive containing SSH keys?
- What will you do if someone transfers your SSH keys to another device without your consent?
- What can you do if someone isn't trustworthy got access to the disk drive?
- What can happen if you have forgotten to delete the SSH keys after sharing the disk drive?
If you compromise your SSH keys, it is no surprise that your business can end in no time.
Do not share your SSH keys via email or chat applications
During a production outage, you may need assistance from other team members to debug or troubleshoot servers. Sometimes you may copy-paste SSH key data over third-party apps like Gmail, Slack, Google Hangout, WhatsApp, Skype, etc., to share it with your team member. Once you do this, your SSH key gets stored on those third-party services databases. Later, the same SSH key data can be copied and misused by anyone from your team. There are high chances for your SSH key data to be compromised if any security breach happens on those third-party apps/services.
Blindly trusting third-party services/apps can be a disaster for you in the future.
Need a solution for the SSH key sharing problem? Try SloopEngine
With SloopEngine's centralized SSH key management, you can securely store, manage, and rotate SSH keys for every environment like production, staging, development, etc. All the SSH keys are encrypted and stored using SloopEngine's centralized SSH key management. Due to the adoption of cloud servers, it's a must for any organization or team to centrally manage SSH keys because of the security risks associated with them.
Have you got any questions on SloopEngine's centralized SSH key management? Let us know in the comment section below. Our team is willing to provide a personalized demo to you if you believe that SloopEngine is the right choice for your organization.